原文地址:https://lala.im/8486.html,請支持原作者!該處僅作轉載。
这篇文章记录一下用verysimple配置一个trojan协议的代理,并使用nginx的ngx_stream_ssl_preread模块进行sni分流。首先安装需要用到的包:
apt -y update
apt -y install xz-utils curl nginx下载verysimple:
mkdir -p /usr/local/etc/verysimple
curl -L https://github.com/e1732a364fed/v2ray_simple/releases/download/v1.2.4-beta.2/verysimple_linux_amd64.tar.xz -o verysimple_linux_amd64.tar.xz
tar xf verysimple_linux_amd64.tar.xz -C /usr/local/etc/verysimple
mv /usr/local/etc/verysimple/verysimple /usr/local/bin新建systemd服务:
nano /etc/systemd/system/verysimple.service写入如下配置:
[Unit]
Description=verysimple service
Documentation=https://github.com/e1732a364fed/v2ray_simple
After=network.target
[Service]
CapabilityBoundingSet=CAP_NET_ADMIN CAP_NET_BIND_SERVICE
AmbientCapabilities=CAP_NET_ADMIN CAP_NET_BIND_SERVICE
ExecStart=/usr/local/bin/verysimple -c /usr/local/etc/verysimple/server.toml
Restart=on-failure
RestartSec=1800s
LimitNOFILE=infinity
[Install]
WantedBy=multi-user.target新建一个verysimple的配置文件:
nano /usr/local/etc/verysimple/server.toml写入如下配置:
[[listen]]
protocol = "trojans"
uuid = "036514da-75fd-4e36-9ca9-229617fd3b4c"
ip = "127.0.0.1"
host = "trojan.example.com"
port = 62000
sniffing.enabled = true
cert = "/usr/local/etc/verysimple/trojan.example.com.pem"
key = "/usr/local/etc/verysimple/trojan.example.com.key"
insecure = false
extra = { tls_minVersion = "1.2" }
xver = 2
fullcone = true
[[fallback]]
dest = 23333
xver = 2
[[dial]]
protocol = "direct"
fullcone = true启动verysimple并设置开机自启:
systemctl enable --now verysimple编辑nginx的主配置文件:
nano /etc/nginx/nginx.conf写入如下配置:
stream {
map $ssl_preread_server_name $verysimple {
trojan.example.com trojan;
}
upstream trojan {
server 127.0.0.1:62000;
}
server {
listen 443 reuseport;
listen [::]:443 reuseport;
proxy_pass $verysimple;
ssl_preread on;
proxy_protocol on;
}
}新建一个nginx站点配置文件,用于回落站点:
nano /etc/nginx/conf.d/fallback.conf写入如下配置:
server {
listen 80;
server_name trojan.example.com;
if ($host = trojan.example.com) {
return 301 https://$host$request_uri;
}
return 404;
}
server {
listen 127.0.0.1:23333 proxy_protocol;
set_real_ip_from 127.0.0.1;
real_ip_header proxy_protocol;
server_name trojan.example.com;
index index.html;
root /var/www/html/flappyfrog;
}重载nginx使配置生效:
systemctl reload nginx服务端至此全部配置完成,在这里下载客户端:https://github.com/e1732a364fed/v2ray_simple/releases
建议目前先下载v1.2.4-beta.2版本使用。verysimple客户端的配置:
[[listen]]
protocol = "socks5"
host = "127.0.0.1"
port = 50800
sniffing.enabled = true
[[dial]]
tag = "proxy"
protocol = "trojans"
uuid = "036514da-75fd-4e36-9ca9-229617fd3b4c"
host = "trojan.example.com"
port = 443
insecure = false
utls = true
use_mux = true
[[dial]]
tag = "direct"
protocol = "direct"
[[route]]
country = ["CN"]
ip = ["private"]
domain = ["geosite:cn"]
toTag = "direct"因为配置了route,需要用到GeoLite2-Country.mmdb和geosite,先启动一次加上-d参数让程序把这些文件下载下来:
cd C:\Users\LALA\Desktop\verysimple
.\verysimple.exe -c trojan.client.toml -d之后退出再运行即可:
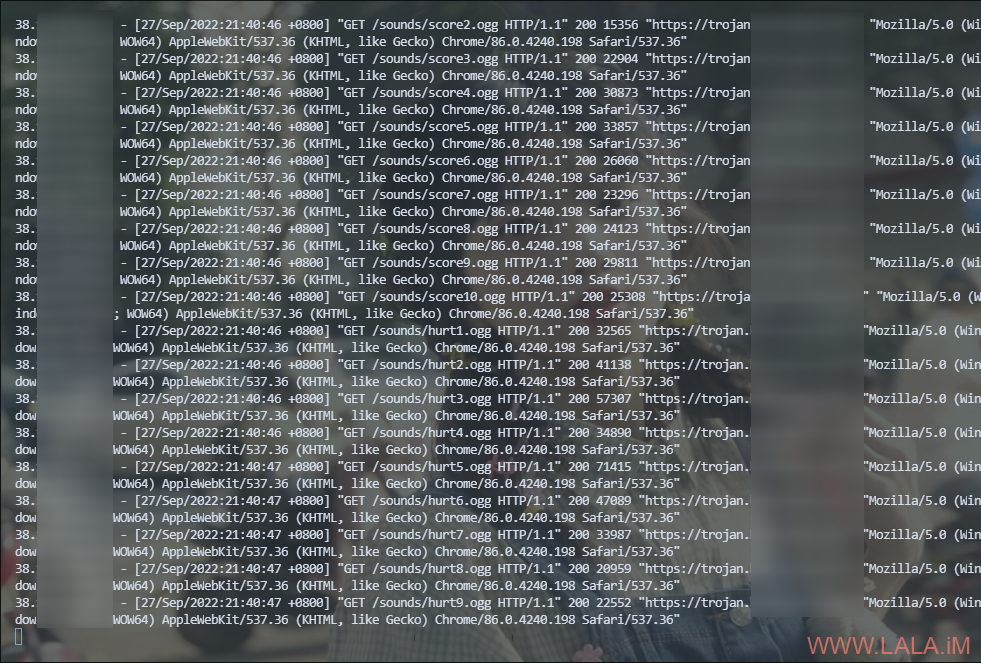
.\verysimple.exe -c trojan.client.tomlverysimple的fallback功能很完善,支持proxy_protocol,所以回落站点可以获取到真实的访客ip,用浏览器访问一下你的域名,再看看nginx的access日志即可发现记录的ip是真实ip: